
This course covers the duties of those who are responsible for monitoring and detecting security incidents in information systems and networks, and for executing a proper response to such incidents. Depending on the size of the organization, this individual may act alone or may be a member of a computer security incident response team (CSIRT). The course introduces strategies, frameworks, methodologies, and tools to manage cybersecurity risks, identify various types of common threats, design and operate secure computing and networking environments, assess and audit the organization’s security, collect and analyze cybersecurity intelligence, and handle incidents as they occur. The course also covers closely related information assurance topics such as auditing and forensics to provide a sound basis for a comprehensive approach to security aimed toward those on the front lines of defense.
Course Length: 5 Days
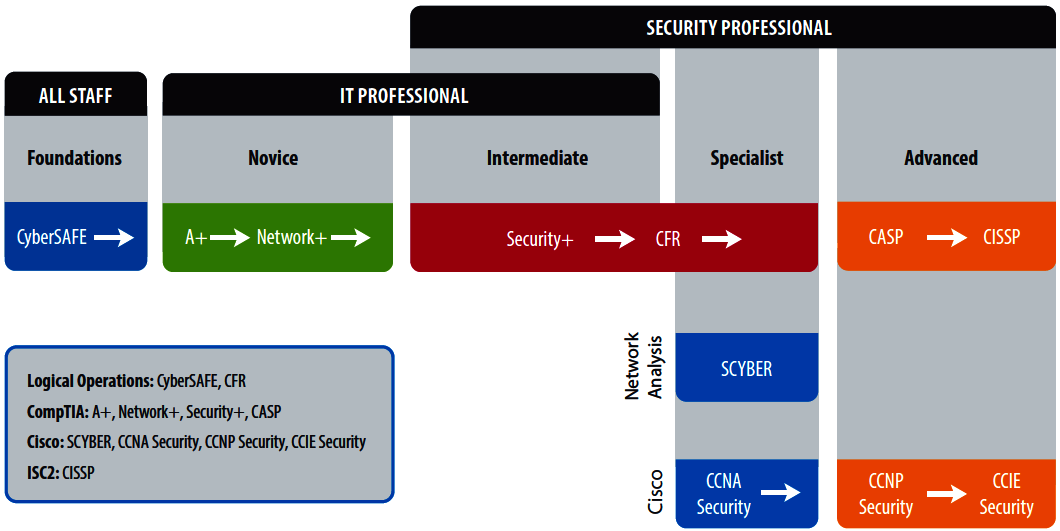
Learning Path: (Click to enlarge)
Course Objectives:
In this course, you will develop, operate, manage, and enforce security capabilities for systems and networks.
You will:











Target audience:
This course is designed for cybersecurity practitioners who perform job functions related to protecting and defending information systems by ensuring their availability, integrity, authentication, confidentiality, and non-repudiation. This course focuses on the knowledge, ability, and skills necessary to provide for the restoration of those information systems in a cybersecurity context including protection, detection, investigation, reaction, response, and auditing capabilities.
This course is also designed to assist students in preparing for the CyberSec First Responder: Threat Detection and Response (Exam CFR-101) certification examination. What you learn and practice in this course can be a significant part of your preparation.
In addition, this course can help students who are looking to fulfill DoD directive 8570.01 for information assurance (IA) training. This program is designed for personnel performing IA functions, establishing IA policies and implementing security measures and procedures for the Department of Defense and affiliated information systems and networks.
Prerequisites:
To ensure your success in this course you should have the following requirements:






You can obtain this level of skills and knowledge by taking the following Logical Operations courses or by passing the relevant exams:



Lesson 1: Assessing Information Security Risk
Topic A: Identify the Importance of Risk Management
Topic B: Assess Risk
Topic C: Mitigate Risk
Topic D: Integrate Documentation into Risk Management
Lesson 2: Creating an Information Assurance Lifecycle Process
Topic A: Evaluate Information Assurance Lifecycle Models
Topic B: Align Information Security Operations to the Information Assurance Lifecycle
Topic C: Align Information Assurance and Compliance Regulations
Lesson 3: Analyzing Threats to Computing and Network Environments
Topic A: Identify Threat Analysis Models
Topic B: Assess the Impact of Reconnaissance Incidents
Topic C: Assess the Impact of Systems Hacking Attacks
Topic D: Assess the Impact of Malware
Topic E: Assess the Impact of Hijacking and Impersonation Attacks
Topic F: Assess the Impact of DoS Incidents
Topic G: Assess the Impact of Threats to Mobile Security
Topic H: Assess the Impact of Threats to Cloud Security
Lesson 4: Designing Secure Computing and Network Environments
Topic A: Information Security Architecture Design Principles
Topic B: Design Access Control Mechanisms
Topic C: Design Cryptographic Security Controls
Topic D: Design Application Security
Topic E: Design Computing Systems Security
Topic F: Design Network Security
Lesson 5: Operating Secure Computing and Network Environments
Topic A: Implement Change Management in Security Operations
Topic B: Implement Monitoring in Security Operations
Lesson 6: Assessing the Security Posture Within a Risk Management Framework
Topic A: Deploy a Vulnerability Management Platform
Topic B: Conduct Vulnerability Assessments
Topic C: Conduct Penetration Tests on Network Assets
Topic D: Follow Up on Penetration Testing
Lesson 7: Collecting Cybersecurity Intelligence Information
Topic A: Deploy a Security Intelligence Collection and Analysis Platform
Topic B: Collect Data from Security Intelligence Sources
Lesson 8: Analyzing Cybersecurity Intelligence Information
Topic A: Analyze Security Intelligence to Address Incidents
Topic B: Use SIEM Tools for Analysis
Lesson 9: Responding to Cybersecurity Incidents
Topic A: Deploy an Incident Handling and Response Architecture
Topic B: Perform Real-Time Incident Handling Tasks
Topic C: Prepare for Forensic Investigation
Lesson 10: Investigating Cybersecurity Incidents
Topic A: Create a Forensic Investigation Plan
Topic B: Securely Collect Electronic Evidence
Topic C: Identify the Who, Why, and How of an Incident
Topic D: Follow Up on the Results of an Investigation
Lesson 11: Auditing Secure Computing and Network Environments
Topic A: Deploy a Systems and Processes Auditing Architecture
Topic B: Prepare for Audits
Topic C: Perform Audits Geared Toward the Information Assurance Lifecycle
Our fees are as follows for students living in UK or the European Union:
CyberSec First Responder |
FEE |
| Full Course (can be paid in instalments) | £3000 |
Fees are payable in advance at the start of course unless otherwise agreed.
We also provide flexible fee instalments to help students in paying their fee.
Contact the college for more details.